High quality latest CompTIA Security+ SY0-401 dumps exam real questions and answers free download from leads4pass. Practice for your CompTIA Security+ SY0-401 exam with the help of leads4pass, at leads4pass you can find all the necessary things for yourself that will help you to pass CompTIA SY0-401 exam.
“CompTIA Security+ Certification” is the name of CompTIA Security+ https://www.leads4pass.com/sy0-401.html exam dumps which covers all the knowledge points of the real CompTIA exam. You can download CompTIA Security+ SY0-401 dumps pdf training material from leads4pass and pass the CompTIA SY0-401 exam in the first attempt. CompTIA Security+ SY0-401 dumps exam preparation kit contains all the necessary SY0-401 questions that you need to know.
【Latest CompTIA SY0-401 dumps pdf materials from google drive】: https://drive.google.com/open?id=0B_7qiYkH83VRMEhpY1lTQnR4NDA
【Latest CompTIA SY0-101 dumps pdf materials from google drive】: https://drive.google.com/open?id=0B_7qiYkH83VRWm1VeWl0ZVhINkk
Vendor: CompTIA
Certifications: Security+
Exam Name: CompTIA Security+ Certification
Exam Code: SY0-401
Total Questions: 1776 Q&As
New CompTIA Security+ SY0-401 Dumps Exam Real Questions And Answers (1-20)
QUESTION 1
Ann, a security administrator, is strengthening the security controls of the company’s campus. Her goal is to prevent people from accessing open locations that are not supervised, such as around the receiving dock. She is also concerned that employees are using these entry points as a way of bypassing the security guard at the main entrance. Which of the following should Ann recommend that would BEST address her concerns?
A. Increase the lighting surrounding every building on campus
B. Build fences around campus with gate entrances
C. Install cameras to monitor the unsupervised areas
D. Construct bollards to prevent vehicle entry in non-supervised areas
Correct Answer: B
QUESTION 2
Mobile tablets are used by employees on the sales floor to access customer data. Ann a customer recently reported that another customer was able to access her personal information on the tablet after the employee left the area. Which of the following would BEST prevent these issues from reoccurring?
A. Screen Locks
B. Full-device encryption
C. Application control
D. Asset tracking
Correct Answer: A
QUESTION 3
A member of a digital forensics team, Joe arrives at a crime scene and is preparing to collect system data.
Before powering the system off, Joe knows that he must collect the most volatile date first. Which of the following is the correct order in which Joe should collect the data?
A. CPU cache, paging/swap files, RAM, remote logging data
B. RAM, CPU cache. Remote logging data, paging/swap files
C. Paging/swap files, CPU cache, RAM, remote logging data
D. CPU cache, RAM, paging/swap files, remote logging data
Correct Answer: B
QUESTION 4
A new employee has been hired to perform system administration duties across a large enterprise comprised of multiple separate security domains. Each remote location implements a separate security domain. The new employee has successfully responded to and fixed computer issues for the main office.
When the new employee tries to perform work on remote computers, the following messages appears.
You need permission to perform this action. Which of the following can be implemented to provide system administrators with the ability to perform administrative tasks on remote computers using their uniquely assigned account?
A. Implement transitive trust across security domains
B. Enable the trusted OS feature across all enterprise computers
C. Install and configure the appropriate CA certificate on all domain controllers
D. Verify that system administrators are in the domain administrator group in the main office
Correct Answer: A
QUESTION 5
An administrator wants to provide onboard hardware based cryptographic processing and secure key storage for full-disk encryption. Which of the following should the administrator use to fulfil therequirements?
A. AES
B. TPM
C. FDE
D. PAM
Correct Answer: B
QUESTION 6
Users in an organization are experiencing when attempting to access certain websites. The users report that when they type in a legitimate URL, different boxes appear on the screen, making it difficult to access the legitimate sites. Which of the following would best mitigate this issue?
A. Pop-up blockers
B. URL filtering
C. Antivirus
D. Anti-spam
Correct Answer: C
QUESTION 7
A security engineer is faced with competing requirements from the networking group and database administrators. The database administrators would like ten application servers on the same subnet for ease of administration, whereas the networking group would like to segment all applications from one another. SY0-401 dumps Which of the following should the security administrator do to rectify this issue?
A. Recommend performing a security assessment on each application, and only segment the applications with the most vulnerability
B. Recommend classifying each application into like security groups and segmenting the groups from one another
C. Recommend segmenting each application, as it is the most secure approach
D. Recommend that only applications with minimal security features should be segmented to protect them
Correct Answer: B
QUESTION 8
Which of the following is an attack designed to activate based on date?
A. Logic bomb
B. Backdoor
C. Trojan
D. Rootkit
Correct Answer: A
QUESTION 9
A security administrator has concerns that employees are installing unapproved applications on their company provide smartphones. Which of the following would BEST mitigate this?
A. Implement remote wiping user acceptance policies
B. Disable removable storage capabilities
C. Implement an application whitelist
D. Disable the built-in web browsers
Correct Answer: C
QUESTION 10
Which of the following is a proprietary protocol commonly used for router authentication across an enterprise?
A. SAML
B. TACACS
C. LDAP
D. RADIUS
Correct Answer: B
QUESTION 11
After a new RADIUS server is added to the network, an employee is unable to connect to the company’s WPA2-Enterprise WIFI network, which is configured to prompt for the employee’s network username and password. The employee reports receiving an error message after a brief connection attempt, but is never prompted for credentials. Which of the following issues could be causing the problem?
A. The employee’s account is locked out in the directory service
B. The new RADIUS server is overloading the wireless access point
C. The new RADIUS server’s certificate is not trusted by the employee’s PC
D. The employee’s account is disabled in the RADIUS server’s local database
Correct Answer: A
QUESTION 12
A security analyst has been asked to perform a review of an organization’s software development lifecycle.
The analyst reports that the lifecycle does not contain a phase in which team members evaluate and provide critical feedback of another developer’s code. Which of the following assessment techniques is BEST described in the analyst’s report?
A. Architecture evaluation
B. Baseline reporting
C. Whitebox testing
D. Peer review
Correct Answer: D
QUESTION 13
The helpdesk is receiving numerous reports that a newly installed biometric reader at the entrance of the data center has a high of false negatives. Which of the following is the consequence of this reported problem?
A. Unauthorized employees have access to sensitive systems
B. All employees will have access to sensitive systems
C. No employees will be able to access the datacenter
D. Authorized employees cannot access sensitive systems
Correct Answer: C
QUESTION 14
Joe, a security technician, is configuring two new firewalls through the web on each. Each time Joe connects, there is a warning message in the browser window about the certificate being untrusted. Which of the following will allow Joe to configure a certificate for the firewall so that firewall administrators are able to connect both firewalls without experiencing the warning message?
A. Apply a permanent override to the certificate warning in the browser
B. Apply a wildcard certificate obtained from the company’s certificate authority
C. Apply a self-signed certificate generated by each of the firewalls
D. Apply a single certificate obtained from a public certificate authority
Correct Answer: C
QUESTION 15
Joe a computer forensic technician responds to an active compromise of a database server. Joe first collects information in memory, then collects network traffic and finally conducts an image of the hard drive. Which of the following procedures did Joe follow?
A. Order of volatility
B. Chain of custody
C. Recovery procedure
D. Incident isolation
Correct Answer: A
QUESTION 16
A company has a BYOD policy that includes tablets and smart phones. In the case of a legal investigation, which of the following poses the greatest security issues? SY0-401 dumps
A. Recovering sensitive documents from a device if the owner is unable or unwilling to cooperate
B. Making a copy of all of the files on the device and hashing them after the owner has provided the PIN
C. Using GPS services to locate the device owner suspected in the investigation
D. Wiping the device from a remote location should it be identified as a risk in the investigation
Correct Answer: A
QUESTION 17
The IT department needs to prevent users from installing untested applications. Which of the following would provide the BEST solution?
A. Job rotation
B. Least privilege
C. Account lockout
D. Antivirus
Correct Answer: B
QUESTION 18
An administrator uses a server with a trusted OS and is configuring an application to go into production tomorrow, In order to make a new application work properly, the administrator creates a new policy that labels the application and assigns it a security context within the trusted OS. Which of the following control methods is the administrator using by configuring this policy?
A. Time based access control
B. Mandatory access control
C. Role based access control
D. Rule based access control
Correct Answer: C
QUESTION 19
A security administrator suspects that an employee in the IT department is utilizing a reverse proxy to bypass the company’s content filter and browse unapproved and non-work related sites while at work.
Which of the following tools could BEST be used to determine how the employee is connecting to the reverse proxy?
A. Port scanner
B. Vulnerability scanner
C. Honeypot
D. Protocol analyzer
Correct Answer: C
QUESTION 20
Joe notices there are several user accounts on the local network generating spam with embedded malicious code. Which of the following technical control should Joe put in place to BEST reduce these incidents?
A. Account lockout
B. Group Based Privileges
C. Least privilege
D. Password complexity
Correct Answer: A
Useful latest CompTIA Security+ SY0-401 dumps exam practice files and study guides in PDF format free download from leads4pass. The best and most updated latest CompTIA Security+ https://www.leads4pass.com/sy0-401.html dumps pdf training resources which are the best for clearing SY0-401 exam test, and to get certified by CompTIA Security+. Download CompTIA Security+ SY0-401 dumps exam questions and verified answers. 100% passing guarantee and full refund in case of failure.
What Our Customers Are Saying:
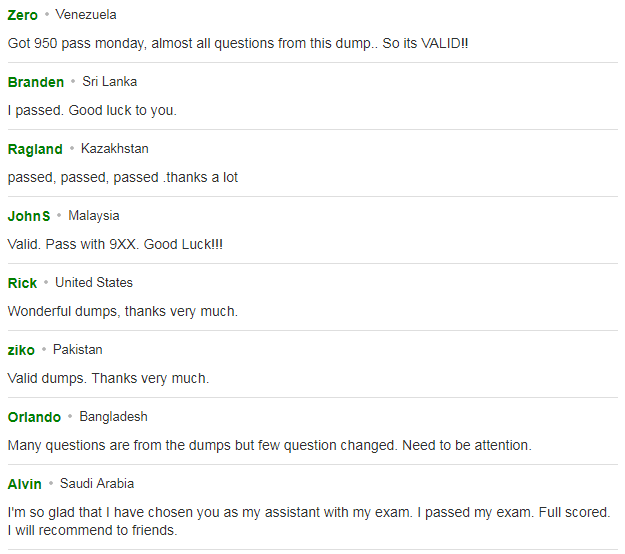
You can click here to have a review about us: https://www.resellerratings.com/store/leads4pass
Why Select leads4pass?
leads4pass is the best site for providing online preparation material for SY0-401 exam. Get your CompTIA Security+ SY0-401 exam prep questions in form of SY0-401 PDF. Other brands started earlier, but the questions are outdated and the price is relatively expensive. leads4pass provide the latest real and cheapest practice questions and answers, help you pass the exam easily at first try.